Companies Need to Stay Vigilant Against Hackers

Charlie Christianson says small companies should not assume their size protects them from hacker attacks.
It turns out Target wasn’t the only … well, target.
A year ago, Target announced that hackers had stolen personal information from some 110 million customer accounts. A handful of similarly high-profile breaches followed, including the breach of some 83 million JPMorgan Chase accounts in August and financial data from 56 million Home Depot customers in September.
Other high-profile victims of cybercrime in 2014 included Staples, Healthcare.gov, Neiman Marcus, and, of course, Sony, which endured the release of e-mails that strained relationships across the entertainment industry.
But those are major corporations, household names. The smaller companies that dot Western Mass. don’t have to worry about such attacks, right?
Think again.
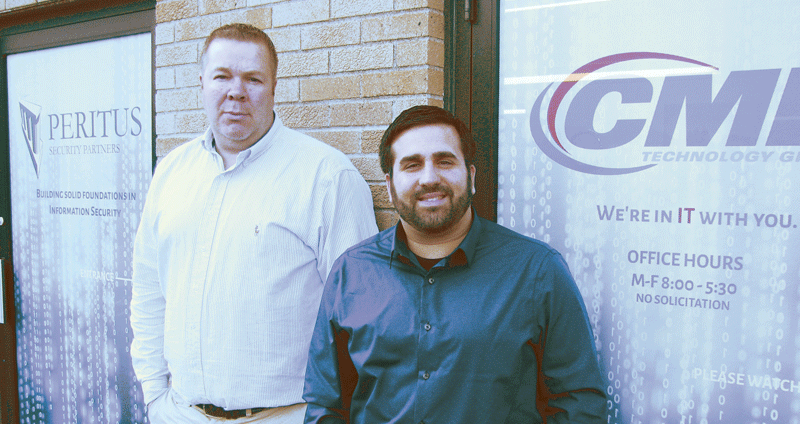
“Small to medium-sized businesses tune out because they think, ‘I’m just too small; no one’s going to want to attack me.’ The reality is, attacks on soft targets are going up astronomically every day,” said Charlie Christianson, president and CEO of Peritus Security Partners and CMD Technology Group.
“We want businesses to understand that there’s no magic bullet, no one product or solution that’s going to eliminate all the security risks,” he added. “Defenses need to be layered, and you have to include your people in the process. You’ve got to educate the people using your systems and make sure the culture in your organization is security-centric, and that everyone understands the risks that are out there.”
James Baker, lead security consultant for Peritus, agreed.
“Those are extreme cases,” he said of cases like Target and Sony, “but people shouldn’t have the attitude that ‘it won’t happen to me.’ A lot of hackers go after low-hanging fruit; they’re not focusing on a specific company or organization. Maybe your firewalls are misconfigured, and someone’s doing a scan, looking for certain ports open, and all of a sudden you pop up. It can be done fairly easily. It’s not a direct attack on your organization — it’s about low-hanging fruit, and your fruit is exposed.”
Although awareness is growing of the threats, he added, smaller companies often figure it’s not worth investing scarce resources into hiring a full-time cybersecurity professional or using a consultant.
“They think, ‘we don’t find a significant need for this. Why would we want to budget money on something we don’t feel we need?’” Baker told BusinessWest. “But once people do get compromised, they become very reactionary. Target did not have a CISO [chief information-security officer]; they did not have a security representative in the executive organization. Since this happened, they hired a brand-new CISO and compliance officer, who have that voice in management.
“But at smaller companies, where budgets are tight and personnel are overworked, they just go to the IT person whose responsibility is to keep the organization running, thinking, ‘he understands security.’
“We see that a lot,” Christianson added, “especially in small companies, where one person in the house has a little tech savvy and they’re the guy or woman who handles everything, who wears a whole bunch of hats. They put out the fires as they exist, and although they give it their best shot, security is not what they do. They don’t understand what the best practices are; they don’t understand all the things you need to do to secure an organization.”
For this issue’s focus on security, BusinessWest explores the reasons why that mindset is changing at many companies — sometimes, unfortunately, after the damage is done.
Head in the Cloud
One major change that has complicated cybsersecurity is the fact that so much data is stored in the cloud and shared among remote devices, said Dave DelVecchio, owner of Innovative Business Systems in Easthampton. He believes companies need to take a hard look at how data is shared and where, with the goal of “letting the good guys in and keeping the bad guys out.”
For example, “if you’re a 40-, 50-, or 100-person company, whether you have an internal IT department or outsource to a company like us, what are the appropriate safeguards to put in place if you want to allow remote access on company-owned devices?” he asked. “Now that employees have more technology in their hands, and they want to store their calendars and contacts on their smartphone, what if a device is stolen or falls into the wrong hands?”
Mark Jardim (right, with James Baker) says that, when it comes to remote access, companies must strike a balance between employee convenience and protecting data.
The question companies need to ask is what benefit they’re getting from allowing remote sharing of data. “I think it’s important to go back and see what people are trying to accomplish. The goal of working with technology in any business is to improve efficiencies and be able to get more done with less. That goal hasn’t changed in 40, 50 years, since ENIAC, in fact,” he said, referring to the first computer, built in the 1940s.
“Ultimately, what really matters is providing a secure and stable user environment to allow users access to technology to allow them to do their jobs,” he went on. “Employers need to decide whether allowing sensitive data on [remote] devices helps them achieve those efficiencies, and if so, they need to make sure employees understand how to protect that data.”
Baker agreed. “Years ago, there was a perimeter around your infrastructure to protect you. But that perimeter is gone. With the cloud and mobile devices and the need for businesses to virtualize and have information in the cloud, the idea of having a perimeter around your infrastructure to protect your assets is going away,” he told BusinessWest.
More important, he said, is the human element — educating employees in best practices to protect data, whether that’s creating strong passwords and storing them properly or restricting company-wide access to certain records. “Whether they work for a hospital dealing with patient records or they’re handling credit-card information, your employees have got to understand the data they’re working with, how to protect it, and what are the tools in their repertoire to assist in that.”
Mark Jardim, lead engineer for CMD, said companies can’t secure data without knowing where it is. “We see laptops out in the field, and they have Dropbox, and the person is saving all his stuff there, maybe synching the laptop to work, and it’s not encrypted. Now he has all this data, not encrypted, not backed up. What happens if someone steals or hacks the computer?”
One common hacker ploy is to break into a device, encrypt important data, and extort the victim for money — often hundreds or thousands of dollars — to unencrypt it. “A police department in Massachusetts got infected with malware and actually paid the hacker money to get the data back,” Jardim said.
Christianson said his company recently tested a client’s employees by creating an e-mail that looked like it came from an internal source but was actually a faux phishing scam. “When they clicked the link, it took them to a bogus webpage that looked like the organization’s webpage, where they were asked to enter their name and password.” Thirty percent of the recipients gave up their data.
“People opened the e-mail thinking it was from a trusted resource,” Baker said. “That is where education and awareness come into play. You can explain to them what happened and how they were tricked and how they can protect themselves in the future.”
Because of the sophistication of hackers and phishing scams, Jardim concedes that today’s environment is much more of a minefield for companies. “Before, you had a firewall, and everything was behind the firewall. Now you have data everywhere, and you have to find a good balance between user convenience and protecting that data.”
Compliance and Common Sense
DelVecchio noted that companies in regulated industries, like finance and healthcare, face a strict regulatory environment that guides their cybersecurity decisions and, in many cases, forces them to employ compliance and security personnel. But for other types of business, it’s a gray area.
“The industry is a big determining factor in how they define their security and remote-access plan,” he said. “But for any business, regardless of industry, there should be a plan. If you fail to plan, you plan to fail — it’s an old, silly line, but it’s true in this case.”
Even with the Sony hack, which didn’t necessarily threaten regulated data, “they got into sensitive e-mails,” Christianson said, “and now all these stars are getting this information about what people are saying behind their backs. It affects contract negotiations and all kinds of things.”
Jardim said the fundamentals are still strong passwords, strong firewalls, and lots of education. “The easiest way to get a lot of the risk out is to have good practices in place. When JPMorgan recently got hacked, basically, one of their servers didn’t have two-factor authentication. What’s scary is, JPMorgan spent $250 million on secure systems. But, because of one small mistake, they got violated. Best practices were overlooked.”
Christianson agreed, noting that the security of an entire system is only as good as the weakest point.
“Security companies have to be right 100% of the time,” Baker added. “A hacker only has to be right 1% of the time.”
And the threats come from everywhere, he noted. “Somebody from Canada can hack you as easily as a 15-year-old in the Philippines practicing his hacking skills, or the guy next door. There are no boundaries. And to think you can call some sort of law enforcement to assist in this is a bit naïve. If you’re a Home Depot where billions of dollars are involved, the federal government will get involved, but otherwise, it’s not significant enough in cost. They have much bigger fish to fry.”
For the hacked organization, however, it’s a very big deal. The Target attack cost the company $148 million and affiliated financial institutions $200 million. In Home Depot’s case, those figures were $62 million and $90 million, respectively. For small companies, the cost of cleaning up a breach can be even greater, even though the numbers are much smaller, because budgets are already stretched thin.
“The culture starts at the top, with management or the board of directors,” Baker said. “They play a key role in this. They need to realize this is an important aspect of their organization, that there are consequences if you don’t protect sensitive data.”
In other words, don’t make yourself a target.
Joseph Bednar can be reached at [email protected]