Straight Talk About AI
By Sean Hogan
AI is everywhere right now. I have never seen a new technology move as fast as this. The pace of change is hard to keep up with, and it is already changing how businesses operate on a daily basis.
In our office, we have been using AI across several areas. Like most companies, we started with the basics. We used tools like Chat and Copilot to help with content writing, documentation, and internal processes. These tools helped us build standards and procedures faster than before.
The impact was immediate. Tasks that used to take hours, like drafting documents or editing content, could now be done in a fraction of the time. We used AI to create job descriptions, prepare presentations, and clean up written communication. It did not replace our work, but it removed a lot of the repetitive effort that slows teams down. That was what I would call phase one of AI.
The next step came when we introduced meeting transcription and summaries. We started using Otter to capture our meetings and generate notes automatically. This was a turning point for us. Instead of worrying about who was taking notes or what might be missed, we had a full record of every conversation.
This made our meetings more productive. People could stay focused instead of trying to write everything down. After the meeting, we had clear summaries, action items, and records we could refer back to. It saved time and reduced confusion. It also helped with accountability because everyone could see what was discussed and what needed to happen next.
Sean Hogan
“AI is not just for fun. It can support real marketing efforts, from content creation to visual design to campaign planning. It helps teams move faster and test ideas more easily.”
As useful as that was, AI did not stop there. We quickly moved into what I would call phase two.
AI has become a major force in marketing and design. When we first experimented with AI-generated images and branding, the results were rough. Tools struggled with basic things like spelling and consistency. Logos looked off, and text often did not make sense.
That has changed very quickly. Today, these tools are far more capable. They can generate clean visuals, help brainstorm campaign ideas, and support content creation at scale. My kids actually introduced me to Grok, and we had some fun turning still images into short videos. While that started as entertainment, it showed me how fast the technology was improving.
More importantly, it showed how we could use these tools in a business setting. AI is not just for fun. It can support real marketing efforts, from content creation to visual design to campaign planning. It helps teams move faster and test ideas more easily.
Next Steps
From there, we expanded AI into our broader technology stack. We are no longer using it just for administrative tasks or marketing support. We are using it to improve productivity and efficiency across the business.
One of the biggest changes has been in our help desk operations. We have introduced AI into our tier-one support process. With the help of an AI management layer, we can now resolve and remediate common support tickets using a proprietary AI tool. This allows us to handle routine issues quickly and consistently.
The benefit is clear. Our technicians are no longer tied up with repetitive tickets. They can focus on more complex problems that require deeper expertise. This improves both the quality of our service and the development of our team.
It also allows us to deliver a higher level of support to our clients. Instead of spending time on basic issues, our team can focus on solving bigger challenges and providing more value.
Our most recent addition is an AI-powered auto attendant. This is not the old style phone system that most people are used to. This is an agent that can answer calls, ask the right questions, and gather the information we need to help the client. It acts as the first point of contact and sets the tone for the entire interaction.
This has been a major improvement for both our team and our clients. Instead of sending calls to voicemail, clients can speak to an agent right away. The agent collects the necessary details, understands the request, and documents the conversation. That information is then passed along to the appropriate person or team.
Anyone who has ever had to repeat the same issue to multiple people knows how frustrating that can be. This process reduces that problem. The full conversation and transcript are captured and shared, so the next person already has the context they need. If a client needs to open a support ticket, the agent can guide them through the process step by step. It ensures that all required information is collected up front.
There is also a level of consistency that is hard to achieve otherwise. The agent does not forget to ask key questions. It does not miss details. It does not have a bad day or get distracted.
For years, I have emphasized to our team the importance of collecting and confirming information on every call. Do we have the correct phone number? The right email address? The proper contact details? These are simple things, but they matter. The AI agent handles this every time without fail.
We are also looking ahead at how AI can integrate with other systems, including CRM platforms, ERP systems, and inventory management. The goal is to create a more connected environment where information flows smoothly and processes are more efficient.
Risk and Reward
This is an exciting time to be in technology. AI represents a major shift, and we are choosing to embrace it.
That said, AI is not without risk. You need to be careful with how you handle data and personal information. Security and privacy should always be a priority. AI tools are powerful, but they need to be used responsibly. That is a much larger topic and one worth discussing in detail on its own.
AI is not perfect, but it is very capable. It can handle complex tasks, support decision making, and free up time for more important work. The key is to use it as a tool. Challenge it. Test it. Find ways to apply it that make your business stronger and more efficient. If you ignore it, you will fall behind. If you use it wisely, it can give you a real advantage.
One last note: I still write my own blogs. But once I am done, I run them through AI to proofread and clean things up. It turns out AI is pretty good at that, too.
Sean Hogan is president of Hogan Technology Inc.



































 A UMass Amherst sleep scientist, funded with $6.7 million in grants from the National Institutes of Health (NIH), has launched two unprecedented studies that will track over time the brain development of infants and preschoolers to confirm the role of napping in early life and to identify the bioregulatory mechanisms involved.
A UMass Amherst sleep scientist, funded with $6.7 million in grants from the National Institutes of Health (NIH), has launched two unprecedented studies that will track over time the brain development of infants and preschoolers to confirm the role of napping in early life and to identify the bioregulatory mechanisms involved.






















 Women’s Health agrees, adding that “testers loved the huge choice of workouts available, from strength sessions to yoga to meditation, and found it easy to filter classes on the app by duration and difficulty to find the right one for them. Our team also said they were persuaded to push beyond their usual limits during each session thanks to motivational instructors, who helped keep their form in check with non-stop helpful pointers — though some testers found them a tad too intense for their liking.”
Women’s Health agrees, adding that “testers loved the huge choice of workouts available, from strength sessions to yoga to meditation, and found it easy to filter classes on the app by duration and difficulty to find the right one for them. Our team also said they were persuaded to push beyond their usual limits during each session thanks to motivational instructors, who helped keep their form in check with non-stop helpful pointers — though some testers found them a tad too intense for their liking.”











 You’ll find no shortage of love for Apple’s newest models as well, the iPhone 13 Pro ($999) and 13 Pro Max ($1,099), which, boast the best cameras and battery life of any iPhone to date, CNET notes, as well as high-end features like the ability to record ProRes videos. “By packing the 13 Pro and 13 Pro Max with features many of us have wanted for years, including a display with a high refresh rate, Apple further defined the difference between its Pro and non-Pro phones. Three years ago, by comparison, the word Pro seemed more of a marketing term than an indication that the phone was any more professional than a regular iPhone.”
You’ll find no shortage of love for Apple’s newest models as well, the iPhone 13 Pro ($999) and 13 Pro Max ($1,099), which, boast the best cameras and battery life of any iPhone to date, CNET notes, as well as high-end features like the ability to record ProRes videos. “By packing the 13 Pro and 13 Pro Max with features many of us have wanted for years, including a display with a high refresh rate, Apple further defined the difference between its Pro and non-Pro phones. Three years ago, by comparison, the word Pro seemed more of a marketing term than an indication that the phone was any more professional than a regular iPhone.” In the laptop world, the Dell XPS 13 Plus (starting at $1,449) “is a sleek computer that’s built around the latest and most powerful Intel Core processors,” Business Insider notes. “In lieu of click buttons, it uses a seamless glass touchpad surface and replaces the function keys with a top row of touch-sensitive function buttons.” In addition, Dell’s updated RapidCharge Express 2.0 technology can charge the battery up to 80% in under an hour. “Innovations like this,” the publication noted, “can benefit users and keep Dell ahead of rivals.”
In the laptop world, the Dell XPS 13 Plus (starting at $1,449) “is a sleek computer that’s built around the latest and most powerful Intel Core processors,” Business Insider notes. “In lieu of click buttons, it uses a seamless glass touchpad surface and replaces the function keys with a top row of touch-sensitive function buttons.” In addition, Dell’s updated RapidCharge Express 2.0 technology can charge the battery up to 80% in under an hour. “Innovations like this,” the publication noted, “can benefit users and keep Dell ahead of rivals.” Need to keep your devices charged in the car? The Baseus USB-C Car Charger ($19) is an inexpensive device with a 65-watt USB-C port that can power up most laptops, according to bestproducts.com. A USB-A charging connector with a maximum power output of 18 watts is also included. “The product has a sleek design with translucent housing, a built-in voltage display, and onboard illumination. It has built-in tech to protect the connected devices from overcharging and overheating.”
Need to keep your devices charged in the car? The Baseus USB-C Car Charger ($19) is an inexpensive device with a 65-watt USB-C port that can power up most laptops, according to bestproducts.com. A USB-A charging connector with a maximum power output of 18 watts is also included. “The product has a sleek design with translucent housing, a built-in voltage display, and onboard illumination. It has built-in tech to protect the connected devices from overcharging and overheating.” Gamers have more options than ever before as well, but for many, PlayStation still reigns supreme. Calling it “the best plug-and-play gaming platform available,” Digital Trends says the PlayStation 5 ($499), boasts “lightning-fast load speeds, a new controller, and a phenomenal lineup of launch titles (including fan favorites and new exclusives).” In fact, the magazine noted that the PS5 not only easily bests the Xbox when it comes to game selection, Sony has now brought backward compatibility into the fold, so the PS5 will be able to play most PS4 games. “The PS5 simply has the best game library out there right now.”
Gamers have more options than ever before as well, but for many, PlayStation still reigns supreme. Calling it “the best plug-and-play gaming platform available,” Digital Trends says the PlayStation 5 ($499), boasts “lightning-fast load speeds, a new controller, and a phenomenal lineup of launch titles (including fan favorites and new exclusives).” In fact, the magazine noted that the PS5 not only easily bests the Xbox when it comes to game selection, Sony has now brought backward compatibility into the fold, so the PS5 will be able to play most PS4 games. “The PS5 simply has the best game library out there right now.” Speaking of new ways to play, “virtual reality might take its time to have its ‘iPhone moment,’ but it is still very much the next big thing for the coolest gadgets,” Spy notes, and no VR device flashes that promise more than the Meta Quest 2 ($299). Without the need for a powerful computer or special equipment, users can simply strap the Quest 2 (formerly Oculus) to their head, pick up the controllers, and move freely in VR space, thanks to its inside-out technology, which uses cameras placed outside the headset to track the users’ movement in the space around them.
Speaking of new ways to play, “virtual reality might take its time to have its ‘iPhone moment,’ but it is still very much the next big thing for the coolest gadgets,” Spy notes, and no VR device flashes that promise more than the Meta Quest 2 ($299). Without the need for a powerful computer or special equipment, users can simply strap the Quest 2 (formerly Oculus) to their head, pick up the controllers, and move freely in VR space, thanks to its inside-out technology, which uses cameras placed outside the headset to track the users’ movement in the space around them. Then there’s the Samsung Freestyle ($799), a new portable entertainment device that combines a projector and smart speaker into one compact package. It supports 1080p projection at up to 100 inches, offers access to a wide variety of streaming apps, and delivers 360-degree sound with built-in Alexa voice control. “The Freestyle stands out from other compact projectors thanks to its rotating cradle that makes it look like a portable spotlight,” Business Insider notes. “It also has automatic picture adjustments that could make it a breeze to set up virtually anywhere. It can even plug into an overhead light socket so you can project onto the floor or a table.”
Then there’s the Samsung Freestyle ($799), a new portable entertainment device that combines a projector and smart speaker into one compact package. It supports 1080p projection at up to 100 inches, offers access to a wide variety of streaming apps, and delivers 360-degree sound with built-in Alexa voice control. “The Freestyle stands out from other compact projectors thanks to its rotating cradle that makes it look like a portable spotlight,” Business Insider notes. “It also has automatic picture adjustments that could make it a breeze to set up virtually anywhere. It can even plug into an overhead light socket so you can project onto the floor or a table.” In the category of hybrid smartwatch, which combines connectivity with traditional watch mechanics, bestproducts.com chooses the Everett Hybrid Smartwatch ($179), calling it a feature-packed device with a built-in, always-on display and heart-rate sensor. “We like that, instead of looking like a tech product, it resembles a classic chronograph timepiece with mechanical hands and a three-button layout.” The stainless-steel timepiece is waterproof up to 30 meters, and it is available in several finishes, with an easy-to-replace band or bracelet.
In the category of hybrid smartwatch, which combines connectivity with traditional watch mechanics, bestproducts.com chooses the Everett Hybrid Smartwatch ($179), calling it a feature-packed device with a built-in, always-on display and heart-rate sensor. “We like that, instead of looking like a tech product, it resembles a classic chronograph timepiece with mechanical hands and a three-button layout.” The stainless-steel timepiece is waterproof up to 30 meters, and it is available in several finishes, with an easy-to-replace band or bracelet. In the market for a drone? “Every year,” BBC Science Focus notes, “the DJI’s Mini series gets smaller and yet more powerful, cramming high-end specs into a lightweight drone that you can chuck in your bag. But with all those improvements comes an eye-watering price, and an increasing fear for your financial status if you crash it.” The DJI Mini 3 Pro ($759) offers advanced obstacle avoidance features, a rotating lens to film in portrait or landscape, 4K video, smart flying features like automatic tracking, and the ability to follow a subject, the site notes. “Despite its higher price, this feels like the perfect drone for beginners, those who like to travel, or really anyone in the market for a lightweight, high-tech drone.”
In the market for a drone? “Every year,” BBC Science Focus notes, “the DJI’s Mini series gets smaller and yet more powerful, cramming high-end specs into a lightweight drone that you can chuck in your bag. But with all those improvements comes an eye-watering price, and an increasing fear for your financial status if you crash it.” The DJI Mini 3 Pro ($759) offers advanced obstacle avoidance features, a rotating lens to film in portrait or landscape, 4K video, smart flying features like automatic tracking, and the ability to follow a subject, the site notes. “Despite its higher price, this feels like the perfect drone for beginners, those who like to travel, or really anyone in the market for a lightweight, high-tech drone.” At the end of an active day, why not wind down by grilling dinner — wherever you are? The BioLite FirePit+ ($249) is a small, efficient fire pit that burns charcoal and wood. More than 50 air jets deliver oxygen to the fire for a uniform temperature and reduced smoke, while a rechargeable battery runs a built-in fan for controlling the fire up to 30 hours, according to PC Magazine. “You can cook on top of the included grill grate for direct contact with the flames or pick up a cast-iron griddle accessory. Bluetooth lets you control the flame intensity and fan speed with your phone, for a smart grilling experience no matter where you are.”
At the end of an active day, why not wind down by grilling dinner — wherever you are? The BioLite FirePit+ ($249) is a small, efficient fire pit that burns charcoal and wood. More than 50 air jets deliver oxygen to the fire for a uniform temperature and reduced smoke, while a rechargeable battery runs a built-in fan for controlling the fire up to 30 hours, according to PC Magazine. “You can cook on top of the included grill grate for direct contact with the flames or pick up a cast-iron griddle accessory. Bluetooth lets you control the flame intensity and fan speed with your phone, for a smart grilling experience no matter where you are.” Sometimes home security means being prepared when the power goes down. The Anker 757 PowerHouse generator ($1,399) is powered by a lithium iron phosphate battery, which is the same type of battery used to power various electric vehicles, and “it’s a beast,” Gear Patrol notes. “Its multiple ports and outlets allow will allow you to simultaneously charge various gadgets, including your laptop, smartphone, and tablets, as well as power larger appliances like a refrigerator, a TV, or multiple outdoor lights.”
Sometimes home security means being prepared when the power goes down. The Anker 757 PowerHouse generator ($1,399) is powered by a lithium iron phosphate battery, which is the same type of battery used to power various electric vehicles, and “it’s a beast,” Gear Patrol notes. “Its multiple ports and outlets allow will allow you to simultaneously charge various gadgets, including your laptop, smartphone, and tablets, as well as power larger appliances like a refrigerator, a TV, or multiple outdoor lights.” Wired has some ideas for making life easier as a pet owner, like the Smarty Pear Leo’s Loo Too Litter Box ($600). “Veterinarians say automatic litter boxes, while convenient, make it tough for owners to keep tabs on their cat’s bathroom trips — which can be useful for flagging any potential illnesses. The Leo’s Loo Too solves this with a built-in sensor that tracks how often your cat goes, along with its weight, and syncs the data to a companion app on your phone.” The device comes with additional features like UV sterilization and radar to keep the box from self-cleaning while the cat is nearby.
Wired has some ideas for making life easier as a pet owner, like the Smarty Pear Leo’s Loo Too Litter Box ($600). “Veterinarians say automatic litter boxes, while convenient, make it tough for owners to keep tabs on their cat’s bathroom trips — which can be useful for flagging any potential illnesses. The Leo’s Loo Too solves this with a built-in sensor that tracks how often your cat goes, along with its weight, and syncs the data to a companion app on your phone.” The device comes with additional features like UV sterilization and radar to keep the box from self-cleaning while the cat is nearby. Speaking of animals, Wired also recommends the Bird Buddy Bird Feeder ($200), which “gives new meaning to bird watching. Not only does this cute little home feed birds, but its battery-powered camera offers a live feed via the connected app. If that’s not entertaining enough, it’ll snap photos of said birds, identify the species, and present a ton of facts about each one.”
Speaking of animals, Wired also recommends the Bird Buddy Bird Feeder ($200), which “gives new meaning to bird watching. Not only does this cute little home feed birds, but its battery-powered camera offers a live feed via the connected app. If that’s not entertaining enough, it’ll snap photos of said birds, identify the species, and present a ton of facts about each one.”

















 When compared to many of the other cool tech gadgets on this list, the Amazon Smart Plug ($25) “might seem underwhelming, but you might be impressed with how much you like this smart-home accessory once you start using it,” according to spy.com. “Head out on vacation and can’t remember if you left a fan or window AC unit running? If it’s plugged into this, you can simply open up your Alexa app and cut off the power. Have a lamp that you love, but it doesn’t work with a smart bulb? Use one of these to make a dumb lamp very, very smart. On top of all that, Alexa has some impressive power-monitoring tools, so that if you have more than one of these around your home, you can figure out which appliances and electronics around the house are costing you the most money, and you can adjust your usage behavior accordingly.”
When compared to many of the other cool tech gadgets on this list, the Amazon Smart Plug ($25) “might seem underwhelming, but you might be impressed with how much you like this smart-home accessory once you start using it,” according to spy.com. “Head out on vacation and can’t remember if you left a fan or window AC unit running? If it’s plugged into this, you can simply open up your Alexa app and cut off the power. Have a lamp that you love, but it doesn’t work with a smart bulb? Use one of these to make a dumb lamp very, very smart. On top of all that, Alexa has some impressive power-monitoring tools, so that if you have more than one of these around your home, you can figure out which appliances and electronics around the house are costing you the most money, and you can adjust your usage behavior accordingly.” Meanwhile, the same site says the Anker Nebula Solar Portable Projector ($520) won’t replace a fancy, 65-inch, 4K HDR TV, “but for those moments when you’re really craving that movie-theater experience at home … you’ll understand why this made our list of cool tech gadgets.” The projector boasts easy setup, too. “Barely bigger than a book, you can point it at a wall and have it projecting a 120-inch, 1080p version of your favorite Netflix movie without needing to configure the picture settings or find a power outlet.”
Meanwhile, the same site says the Anker Nebula Solar Portable Projector ($520) won’t replace a fancy, 65-inch, 4K HDR TV, “but for those moments when you’re really craving that movie-theater experience at home … you’ll understand why this made our list of cool tech gadgets.” The projector boasts easy setup, too. “Barely bigger than a book, you can point it at a wall and have it projecting a 120-inch, 1080p version of your favorite Netflix movie without needing to configure the picture settings or find a power outlet.” Speaking of projectors, the BenQ X1300i 4LED Gaming Projector ($1,299) is being marketed as the first true gaming projector that’s optimized for the PS5 or Xbox Series X. “The 3,000-lumen projector will play 1080p content — so not true 4K content — at extremely low latency, which is needed for competitive gamers,” according to gearpatrol.com. “Additionally, it has built-in speakers and an Android TV operating system, so it functions as any traditional smart TV — but it can create up to a 150-inch screen.”
Speaking of projectors, the BenQ X1300i 4LED Gaming Projector ($1,299) is being marketed as the first true gaming projector that’s optimized for the PS5 or Xbox Series X. “The 3,000-lumen projector will play 1080p content — so not true 4K content — at extremely low latency, which is needed for competitive gamers,” according to gearpatrol.com. “Additionally, it has built-in speakers and an Android TV operating system, so it functions as any traditional smart TV — but it can create up to a 150-inch screen.” Taking tech outdoors is the DJI Mavic Air 2 Drone ($799), which menshealth.com touts for its massive optical sensor, means “the 48-megapixel photos pop and the hyperlap video is 8K — smart futureproofing for when your TV plays catchup. The next-gen obstacle-avoidance sensors, combined with the 34-minutes-long flight time, mean you spend more time shooting killer video and less time dodging trees and buildings.”
Taking tech outdoors is the DJI Mavic Air 2 Drone ($799), which menshealth.com touts for its massive optical sensor, means “the 48-megapixel photos pop and the hyperlap video is 8K — smart futureproofing for when your TV plays catchup. The next-gen obstacle-avoidance sensors, combined with the 34-minutes-long flight time, mean you spend more time shooting killer video and less time dodging trees and buildings.” Smart wallets offer a convenient way to store and transport cash and credit cards while protecting against loss or theft. The Ekster Parliament Smart Wallet ($89) is a smart bifold wallet with RFID coating (to protect against identity theft) and a patented mechanism that ejects cards from its aluminum storage pocket with the press of a button. It has space for at least 10 cards, as well as a strap for carrying cash and receipts, according to bestproducts.com. “Ekster has crafted the wallet from high-quality leather that comes in a multitude of colors. An optional Bluetooth tracker for the wallet is also available. This ultra-thin gadget has a maximum range of 200 feet, and it is powered by light, so it never needs a battery.”
Smart wallets offer a convenient way to store and transport cash and credit cards while protecting against loss or theft. The Ekster Parliament Smart Wallet ($89) is a smart bifold wallet with RFID coating (to protect against identity theft) and a patented mechanism that ejects cards from its aluminum storage pocket with the press of a button. It has space for at least 10 cards, as well as a strap for carrying cash and receipts, according to bestproducts.com. “Ekster has crafted the wallet from high-quality leather that comes in a multitude of colors. An optional Bluetooth tracker for the wallet is also available. This ultra-thin gadget has a maximum range of 200 feet, and it is powered by light, so it never needs a battery.” In the smartwatch category, the Fossil Gen 5 LTE ($349) is the company’s first product in the cellular wearables market, crn.com notes. “The Fossil Gen 5 LTE Touchscreen leverages LTE connectivity from Verizon, the Qualcomm Snapdragon Wear 3100 platform, and Google’s Wear OS to let users make calls and do texting without a mobile phone.” Fossil also makes what bestproducts.com calls the best hybrid smartwatch, the Fossil Latitude HR Hybrid Smartwatch ($195), “a feature-packed hybrid smartwatch with a built-in, always-on display and a heart-rate sensor. We like that, instead of looking like a tech product, it resembles a classic chronograph timepiece with mechanical hands and a three-button layout. The Latitude HR can effortlessly deliver notifications from your phone and keep tabs on your activities.”
In the smartwatch category, the Fossil Gen 5 LTE ($349) is the company’s first product in the cellular wearables market, crn.com notes. “The Fossil Gen 5 LTE Touchscreen leverages LTE connectivity from Verizon, the Qualcomm Snapdragon Wear 3100 platform, and Google’s Wear OS to let users make calls and do texting without a mobile phone.” Fossil also makes what bestproducts.com calls the best hybrid smartwatch, the Fossil Latitude HR Hybrid Smartwatch ($195), “a feature-packed hybrid smartwatch with a built-in, always-on display and a heart-rate sensor. We like that, instead of looking like a tech product, it resembles a classic chronograph timepiece with mechanical hands and a three-button layout. The Latitude HR can effortlessly deliver notifications from your phone and keep tabs on your activities.” “We don’t know who will be more excited about the Furbo Dog Camera ($169), you or your pet,” popsugar.com notes. “You can monitor them through your phone, send them treats when you’re away, and so much more.” The 1080p, full-HD camera and night vision allows users to livestream video to monitor their pet on their phone with a 160-degree wide-angle view, day and night. A sensor also sends push notifications to a smartphone when it detects barking. Users can even toss treats to their dog via the free Furbo iOS/Android app. Set-up is easy — just plug it in to a power outlet using its USB cord, download the Furbo app, and connect to home WiFi.
“We don’t know who will be more excited about the Furbo Dog Camera ($169), you or your pet,” popsugar.com notes. “You can monitor them through your phone, send them treats when you’re away, and so much more.” The 1080p, full-HD camera and night vision allows users to livestream video to monitor their pet on their phone with a 160-degree wide-angle view, day and night. A sensor also sends push notifications to a smartphone when it detects barking. Users can even toss treats to their dog via the free Furbo iOS/Android app. Set-up is easy — just plug it in to a power outlet using its USB cord, download the Furbo app, and connect to home WiFi. “As one of the first companies to make artificial intelligence and voice-recognition technology available to the average person, spy.com notes, “Google is still the top dog when it comes to voice assistants and smart-home platforms. And perhaps its most radical move was the Google Nest Mini ($35), a small and cheap speaker that is fully imbued with the powers to command your smart home. Once you get used to the particular ways of interacting with a voice assistant, it’s rare when you have to raise your voice or repeat yourself to get the Nest Mini to understand you, even when you’re on the other side of the room, half-asleep at 1 a.m., telling it to turn off the lights, shut off the TV, and lock the doors.”
“As one of the first companies to make artificial intelligence and voice-recognition technology available to the average person, spy.com notes, “Google is still the top dog when it comes to voice assistants and smart-home platforms. And perhaps its most radical move was the Google Nest Mini ($35), a small and cheap speaker that is fully imbued with the powers to command your smart home. Once you get used to the particular ways of interacting with a voice assistant, it’s rare when you have to raise your voice or repeat yourself to get the Nest Mini to understand you, even when you’re on the other side of the room, half-asleep at 1 a.m., telling it to turn off the lights, shut off the TV, and lock the doors.” Tired of housework? “If you’re a fan of the iRobot vacuum, then you’ll want to give the iRobot Braava Jet 240 Robot Mop ($180) a try,” popsugar.com asserts. “It will clean your floors when you’re not around, so you have nothing to worry about later.” The device claims to offer precision jet spray and a vibrating cleaning to tackle dirt and stains, and gets into hard-to-reach places, including under and around toilets, into corners, below cabinets, and under and around furniture and other objects, using an efficient, systematic cleaning pattern. It also mops and sweeps finished hard floors, including hardwood, tile, and stone, and it’s ideal for kitchens and bathrooms.
Tired of housework? “If you’re a fan of the iRobot vacuum, then you’ll want to give the iRobot Braava Jet 240 Robot Mop ($180) a try,” popsugar.com asserts. “It will clean your floors when you’re not around, so you have nothing to worry about later.” The device claims to offer precision jet spray and a vibrating cleaning to tackle dirt and stains, and gets into hard-to-reach places, including under and around toilets, into corners, below cabinets, and under and around furniture and other objects, using an efficient, systematic cleaning pattern. It also mops and sweeps finished hard floors, including hardwood, tile, and stone, and it’s ideal for kitchens and bathrooms. Smart glasses are a thing these days, too. Jlab Audio recently introduced its new Jlab JBuds Frames ($49), a device that discretely attaches to a user’s glasses to provide wireless stereo audio on the go. “The JBuds Frames consist of two independently operating Bluetooth wireless audio devices, which include 16mm drivers that produce sound that can only be heard by the wearer, not by others,” according to crn.com. “In addition, the device can easily be detached and mounted on other frames when needed.”
Smart glasses are a thing these days, too. Jlab Audio recently introduced its new Jlab JBuds Frames ($49), a device that discretely attaches to a user’s glasses to provide wireless stereo audio on the go. “The JBuds Frames consist of two independently operating Bluetooth wireless audio devices, which include 16mm drivers that produce sound that can only be heard by the wearer, not by others,” according to crn.com. “In addition, the device can easily be detached and mounted on other frames when needed.” For a next-level experience in eyewear, “virtual reality might be taking its time to have its ‘iPhone moment,’ but it is still very much the next big thing when it comes to the coolest tech gadgets,” spy.com notes, “and there is not a single VR device that flashes that promise more than the Oculus Quest 2 ($349).” Without the need for a powerful computer or special equipment, users can simply strap the Quest 2 to their head, pick up the controllers, and move freely in VR space thanks to its inside-out technology, which uses cameras on the outside of the headset to track movement. “In a time where we don’t have many places to escape to, the Oculus Quest 2 offers up an infinite number of destinations … even if they’re only virtual.”
For a next-level experience in eyewear, “virtual reality might be taking its time to have its ‘iPhone moment,’ but it is still very much the next big thing when it comes to the coolest tech gadgets,” spy.com notes, “and there is not a single VR device that flashes that promise more than the Oculus Quest 2 ($349).” Without the need for a powerful computer or special equipment, users can simply strap the Quest 2 to their head, pick up the controllers, and move freely in VR space thanks to its inside-out technology, which uses cameras on the outside of the headset to track movement. “In a time where we don’t have many places to escape to, the Oculus Quest 2 offers up an infinite number of destinations … even if they’re only virtual.” Another way to escape into another world — albeit one requiring more effort — is the Peloton Bike+ (from $2,495). “Peloton’s updated bike boasts a lustrous, 24-inch-wide screen and a game-changing multi-grip handlebar that lets you always find comfortable position,” menshealth.com notes. “And the best feature just may be auto-follow, which automatically shifts the resistance when the instructor calls for it. Translation: no escape from tough workouts.”
Another way to escape into another world — albeit one requiring more effort — is the Peloton Bike+ (from $2,495). “Peloton’s updated bike boasts a lustrous, 24-inch-wide screen and a game-changing multi-grip handlebar that lets you always find comfortable position,” menshealth.com notes. “And the best feature just may be auto-follow, which automatically shifts the resistance when the instructor calls for it. Translation: no escape from tough workouts.” Speaking of devices with health benefits, the Polar Verity Sense optical heart monitor ($90) can be worn on the arm or temple (for swimming). “It’s designed for people who don’t necessarily wear a wrist-bound fitness tracker or smartwatch, or are doing an exercise that isn’t very friendly to wrist jewelry, like martial arts, swimming, dancing or boxing,” gearpatrol.com notes. “It’s a nifty accessory for people who use Polar Flow, Polar’s free fitness and training app, or wear one of the company’s smartwatches.”
Speaking of devices with health benefits, the Polar Verity Sense optical heart monitor ($90) can be worn on the arm or temple (for swimming). “It’s designed for people who don’t necessarily wear a wrist-bound fitness tracker or smartwatch, or are doing an exercise that isn’t very friendly to wrist jewelry, like martial arts, swimming, dancing or boxing,” gearpatrol.com notes. “It’s a nifty accessory for people who use Polar Flow, Polar’s free fitness and training app, or wear one of the company’s smartwatches.” Meanwhile, gearpatrol.com is also high on the Ring Video Doorbell Pro 2 ($250), the next-generation version of its well-reviewed video doorbell — and it adds two big upgrades. “First, it adds a new radar sensor that enables new 3D motion detection and bird’s-eye-view features; this allows it to better detect and even create a top-down map of the movement taking place in front of your door. And, secondly, the camera has an improved field of view so that it can capture the delivery person’s entire body — head to toe — when they drop off a package.”
Meanwhile, gearpatrol.com is also high on the Ring Video Doorbell Pro 2 ($250), the next-generation version of its well-reviewed video doorbell — and it adds two big upgrades. “First, it adds a new radar sensor that enables new 3D motion detection and bird’s-eye-view features; this allows it to better detect and even create a top-down map of the movement taking place in front of your door. And, secondly, the camera has an improved field of view so that it can capture the delivery person’s entire body — head to toe — when they drop off a package.” Finally, are you looking for great sound for home entertainment? With Sonos Arc ($799), users can “get immersive audio that can fill an entire house in one slim, sleek, ultra-versatile package,” menshealth.com notes. “A whopping 11 drivers power Sonos’ newest soundbar, fueling a surround-sound experience that delivers in all situations, whether you’re playing Halo or watching Avengers: Endgame.”
Finally, are you looking for great sound for home entertainment? With Sonos Arc ($799), users can “get immersive audio that can fill an entire house in one slim, sleek, ultra-versatile package,” menshealth.com notes. “A whopping 11 drivers power Sonos’ newest soundbar, fueling a surround-sound experience that delivers in all situations, whether you’re playing Halo or watching Avengers: Endgame.”











 “What makes LinkedIn even more powerful is that users update their bios regularly, so the connections you are potentially requesting are in the roles they have listed on their bios.”
“What makes LinkedIn even more powerful is that users update their bios regularly, so the connections you are potentially requesting are in the roles they have listed on their bios.”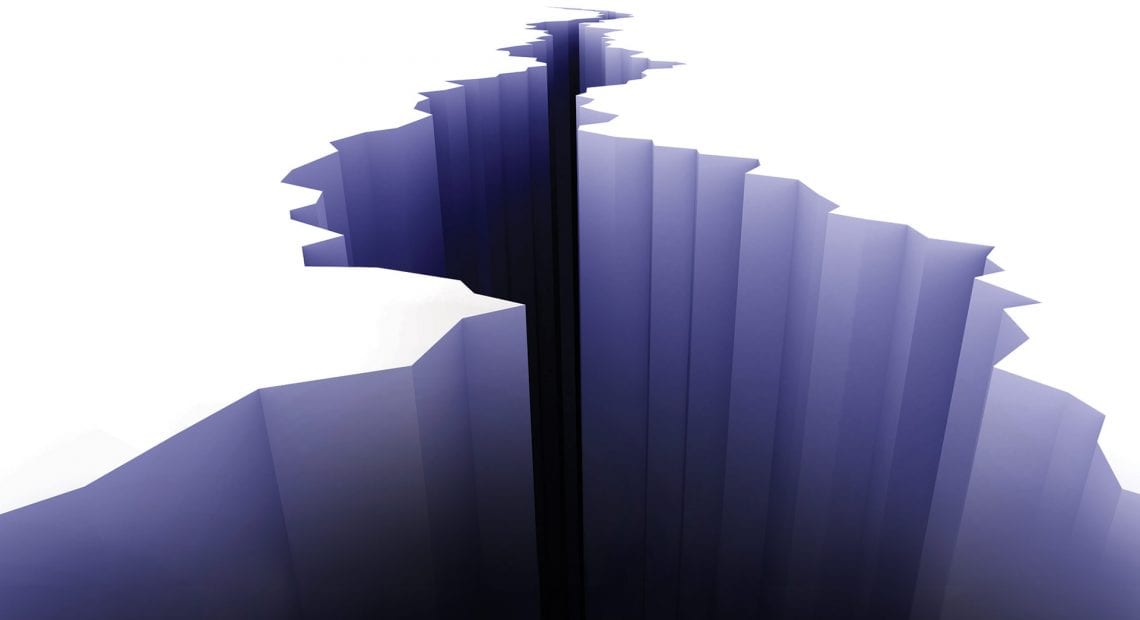
















 Cybersecurity experts say there’s still plenty of misunderstanding when it comes to the reality of data threats. For example, it’s not just big companies being attacked — these days, everyone is a target, and data thieves are becoming more subtle and savvy with their methods. That means companies need to be more vigilant — but it also means career opportunities abound in a field that desperately needs more young talent.
Cybersecurity experts say there’s still plenty of misunderstanding when it comes to the reality of data threats. For example, it’s not just big companies being attacked — these days, everyone is a target, and data thieves are becoming more subtle and savvy with their methods. That means companies need to be more vigilant — but it also means career opportunities abound in a field that desperately needs more young talent.


